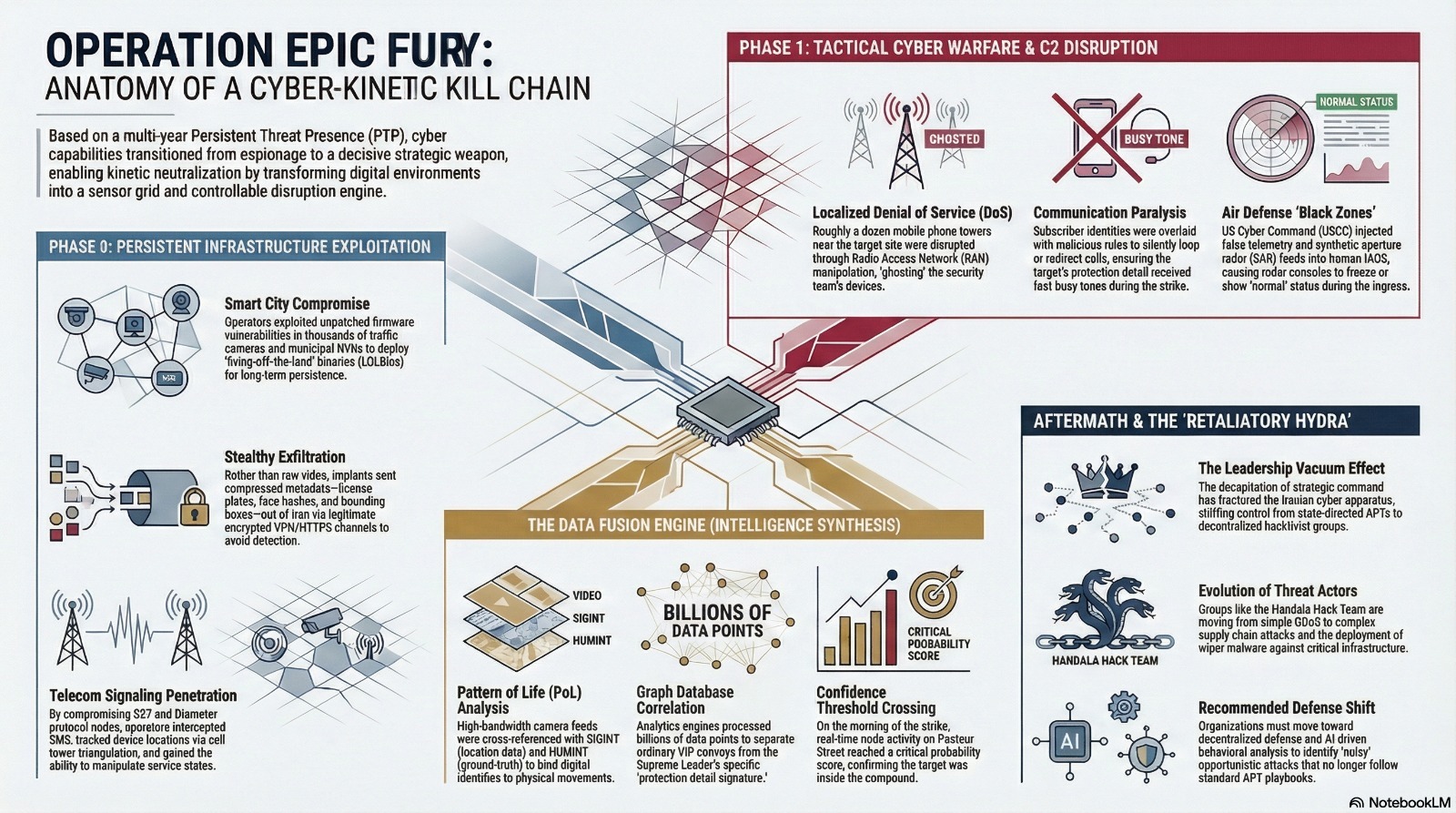
MUMBAI: The operation began long before missile trajectories were plotted; it started years earlier as a slow, methodical intrusion into Tehran’s digital infrastructure. The first targets were not generals or ministries, but the city’s traffic cameras—thousands of weather-stained boxes bolted to poles across junctions and arterial roads, forming the backbone of the capital’s smart traffic system. Their feeds flowed into municipal control rooms and data centres, where software managed congestion, logged violations and increasingly fed Iran’s surveillance apparatus. Somewhere in that chain—camera firmware, NVRs, management consoles—foreign operators found a way in and stayed.
Access did not come through noisy denial-of-service or obvious defacements. It came through precise abuse of weaknesses in firmware and management stacks, the same kinds of flaws security advisories warn about that city IT teams rarely have time to patch. Camera operating systems were quietly re-flashed with modified images that still bore valid vendor signatures and responded correctly to superficial health checks, but contained additional code paths. That code introduced on-device encryption routines wrapping selected frames in strong ciphers using asymmetric keys held only by remote controllers, and lightweight analytics modules running basic object detection directly on devices or their immediate aggregators. In parallel, cameras and recorders were instructed to establish outbound connections indistinguishable from ordinary VPN and HTTPS traffic between municipal sites and central servers.
Over time, nearly all of Tehran’s traffic cameras were reportedly brought under this hidden layer. The exfiltration channel was designed with care; instead of streaming raw video—which would have been noisy and expensive—implants sent heavily compressed clips and structured metadata: timestamps, vehicle detections, license plate strings, face hashes, bounding box coordinates and camera IDs. This data slipped out of Iran along paths used for legitimate encrypted backups and inter-office traffic, terminating in collection points in Tel Aviv and southern Israel.
There, Tehran’s streets became numbers. A multi-source analytics pipeline ingested the hijacked camera feed, much like advanced video-surveillance systems worldwide but tuned for a different mission. GPU-accelerated detection models picked out vehicles, classified them by type and colour, and read plates. Face-recognition systems trained on open-source images of Iranian officials tagged recurring faces with growing confidence. Gait and posture analysis algorithms added a softer biometric layer, recognising certain bodyguards by how they walked, stood at ease or scanned their surroundings.
All of this flowed into a graph database. Each license plate, individual face, distinct handset tied to a person became a node. Edges connected nodes appearing together in space and time: the same SUV with guards at gates, a certain 5-minibus with aides on Friday mornings, bodyguards’ faces entering and leaving Pasteur Street. Cluster-detection algorithms separated ordinary VIP convoys from movements with stricter patterns: smaller circles of personnel, fewer routes, tighter timings, heavier security. One cluster seen repeatedly at the Supreme Leader’s office, residence and religious venues emerged as Ali Khamenei’s protection detail signature.
Meanwhile, a parallel effort unfolded in Iran’s mobile networks. According to Israeli and Western officials, “deep” penetration of mobile systems accompanied the camera operation, giving attackers insight into—and later control over—how calls for specific devices were routed. Using access to core signalling infrastructure, operators queried location information by abusing vulnerabilities in legacy SS7 and Diameter implementations. Those messages revealed which cell towers each phone camped on, movement between sectors and devices traveling in lockstep.
By cross-referencing handset IDs with the camera-derived graph—matching a guard’s face at a gate with the handset appearing in the same sector at the same time—analysts bound digital identities to physical ones. Each guard was no longer just a tall man in a dark suit; he was also an IMSI and IMEI pair with a home cell in a suburb, daily commute path and recurring presence in certain compounds. Over months, the fused system learned weekend duty patterns, shift rotations and route variations; it distinguished genuine convoys from decoys by correlating how many “core” devices and faces moved together.
The occupation of Tehran’s digital terrain deepened in layers. Additional municipal subsystems—parking sensors, access control systems at government buildings, private CCTV feeds linked to city networks—were mapped for context, while passive collection on telecoms links refined movement models. Israeli reportedly used bespoke AI tools and graph-analytics engines to sift through “billions of data points” on Iran’s leadership, continuously updating confidence scores on who was where which routines mattered. By early 2026, Israeli operators could query a visual interface and see, in near real-time, the most probable composition and location of Khamenei’s inner circle on any given day.
On the morning that mattered, the pattern looked different. In late February under heavy geopolitical tension, the system flagged an unusual convergence of the core guard cluster on Pasteur Street. Handsets tied to key bodyguards began moving from residential cells towards the compound before dawn. Traffic-camera nodes along routes lit up in sequence: familiar SUVs and motorcycles captured on fresh video, matching their license plates matching historical high-sensitivity movements. Within the compound, long-controlled foreign cameras registered heightened activity at side gates and inner courtyards with known guards taking positions associated with important meetings.
In Israeli facilities, this appeared as a graph resolving into a familiar shape. Nodes representing key guards and vehicles moved into the Pasteur Street cluster and stayed. Handset-location markers stabilised in inner sectors. Correlation engines compared this configuration against past year’s data, highlighting strong matches with previous instances involving the Supreme Leader personally. Intelligence officers primed by CIA and Mossad HUMINT about a possible leadership conclave now had machine-backed probability figures supporting their judgement that Khamenei was inside.
With that confidence threshold crossed, the cyber campaign flipped from surveillance to disruption. For years, Israeli operators had not only read Iran’s mobile cores but mapped how calls for specific numbers flowed through switches serving the Pasteur area. Now they began altering those flows. Configuration entries for critical subscriber identities—phones carried by guards, aides and command figures—were modified or overlaid with malicious rules. Calls for those numbers were silently looped, dropped or redirected to non-existent endpoints, producing fast busy tones or endless ringing.
At the same time, parameters in the radio access network were nudged. Cell reselection thresholds, handover timers and priority lists for neighbouring sectors adjusted to cause targeted devices to camp on sectors experiencing artificially induced error conditions. The broader city continued seeing usable service—people elsewhere would make calls and refresh social media—but within a small footprint around Pasteur Street, for a specific set of phones inside it, the network degraded sharply at the worst possible moment.
In parallel, American cyber units brought their long-prepared accesses online. US officials acknowledged that Cyber Command had executed operations to “disrupt, degrade and blind” Iranian radar and command networks during the strikes. Malware positioned on routers, firewalls and servers at air-defence sites altered routing tables, corrupted configuration files and flooded control planes with crafted traffic. Radar consoles lagged or froze; track updates came late or not at all; orders between nodes took circuitous paths or failed.
From the outside, news cameras showed only contrails and explosions over Tehran. Inside networks, the effect was a nervous system thrown into disarray. Guards in the Pasteur compound saw and heard something catastrophically wrong—incoming munitions, shockwaves, dust—but their escalation paths were dead. One officer dialled a superior and hit an inexplicable busy tone. Another switched to an alternate number and watched the call hang without connecting. Group chats stalled, secure apps relying on SMS or voice failed to complete handshakes.
Even after the ordnance had done its work, cyber components did not wind down immediately. The same compromised cameras that tracked the guards’ arrival now captured the aftermath: plumes of smoke, emergency vehicles, disrupted movement patterns. Algorithms trained on blast imagery assessed probability of survivability given angle and extent of destruction. In the fused graph, nodes corresponding to core handsets remained dark; no new observations contradicted the working hypothesis that the Supreme Leader had been killed.
On the Iranian side, attempts to restore control ran into lingering digital damage. Senior officers found communications degraded as military and government networks struggled under external attack, internal counter-measures and misconfigured fallbacks. State media websites reported outages or compromises as cyber operations against information outlets continued. For crucial hours after the blast, the regime’s ability to see clearly, talk internally and project authority outward was constrained not just by shock and confusion, but by code sitting quietly inside its infrastructure for years.
In public memory, the assassination of Ali Khamenei will likely be reduced to images of jets, plumes and rubble. In the technical record, it reads as something different: a long disciplined campaign to turn a city’s cameras, switches and base stations into an unwitting sensor and control grid, then on one morning to use that grid to confirm a target, cut his protectors off from the outside world and hold a state’s nervous system in a clenched fist for just long enough to lead.
* Brijesh Singh is a senior IPS officer and an author (@brijeshshingh on X). His latest book on ancient India, “The Cloud Chariot” (Penguin) is out on stands. Views are personal.